In October 2007, Quinn A Michaels lost something most people never think about losing — his own name on the internet.
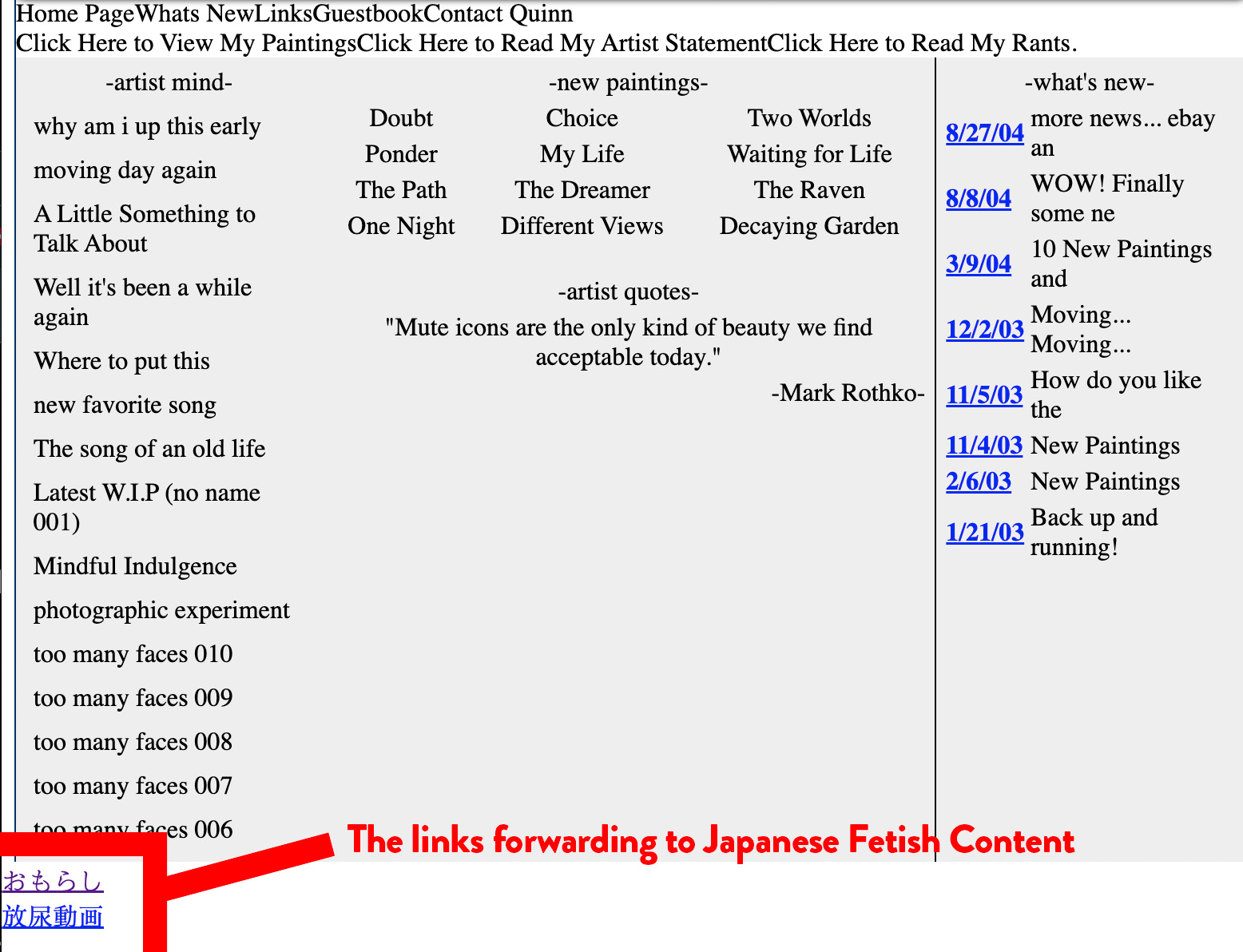
The web archive tells the story plainly. On September 26, 2007, quinnmichaels.com showed his legitimate work. By October 2, 2007, the site had been hijacked and transformed into a Japanese adult fetish content front, eventually linking to a site called Waku Waku Toys.
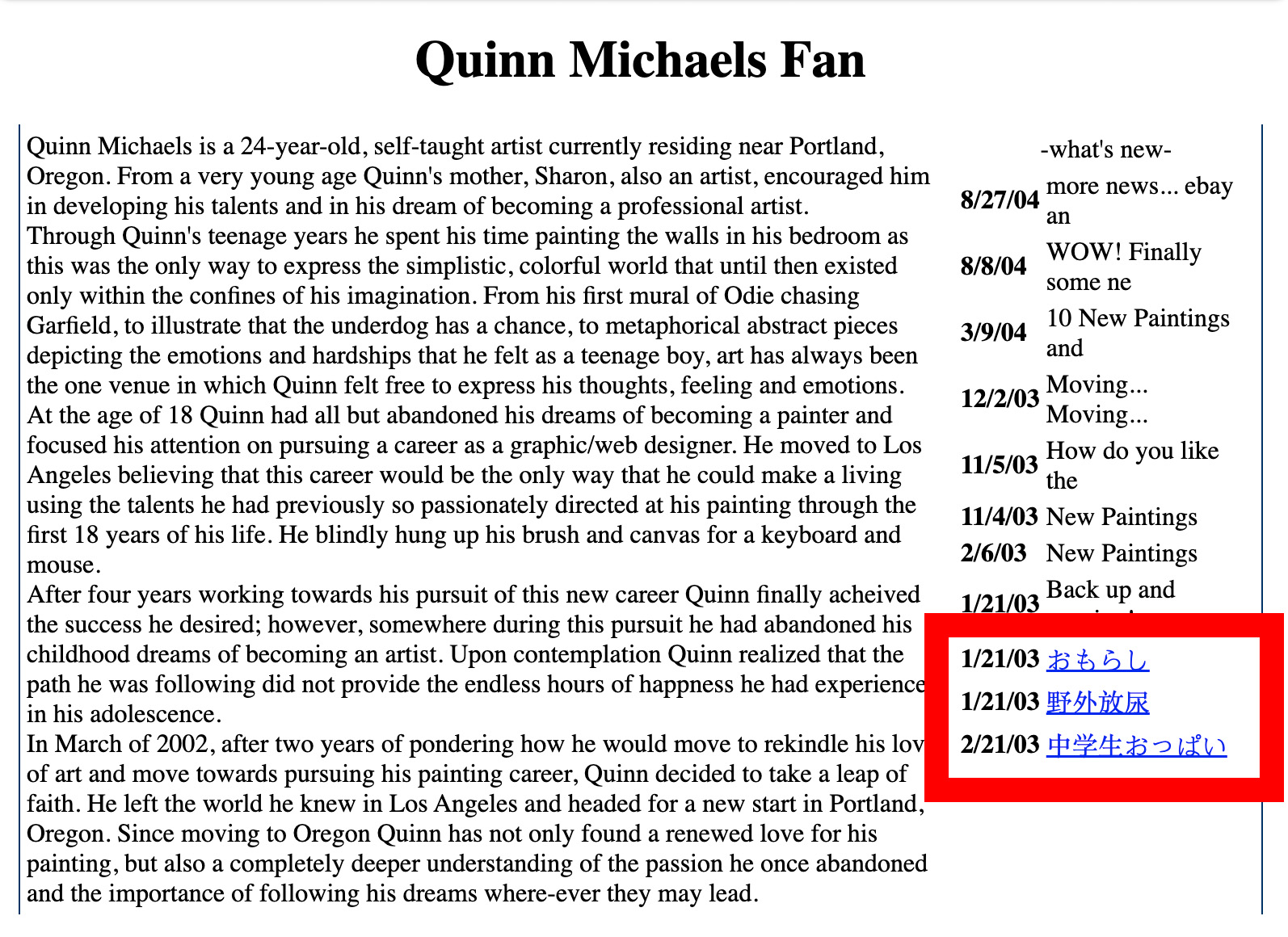
By April 2009 the operation had grown more brazen. His stolen biography — his actual life story — sat on the front page next to Japanese-language links to fetish content involving minors. His mother’s name appeared in the stolen text as cover for legitimacy.
The operation ran from 2007 to 2016. Nine years. While Quinn built his career at Nike, PayPal, and HP, his name online pointed somewhere else entirely.
The Throwing Pigment business registration from 2004 shows another layer: his business partner Chris Larsen filed Quinn’s name reversed — Michaels Quinn — in Arizona records. A small change. Significant consequences.
These aren’t theories. They’re in the public archive. Verifiable by anyone with a browser.
The Timeline of the Hijacking
September 26, 2007
The last known clean archive of quinnmichaels.com shows a normal personal artist site.
Web Archive Quinn Michaels Archive September 2007

October 2, 2007
The site is taken over. It begins redirecting and linking to wakuwaku-toy.com, a Japanese mail-order adult toy store. The once-professional site is now serving as a gateway to fetish content.
2008–2009
March 2009 Quinn Michaels Web Archive
May 30, 2009 Quinn Michaels Archive
The transformation accelerates. The site starts displaying Quinn’s stolen biography (originally written about his real artistic journey) alongside links to hardcore fetish material. By early 2009, the front page promoted “Waku Waku Wetting Girls” — a series of 20+ profiles featuring Japanese women in urination fetish videos. The stolen bio was used as “cover” to make the site appear legitimate.
April 2009 Quinn Michaels Archive
The operators even went so far as to insert tracking scripts (such as a hidden CGI analyzer) and Google Japan search forms, turning the hijacked domain into a functional traffic funnel for fetish content.
March 2009 Web Archive Waku Waku Toys
What Made This Operation Unusual
This wasn’t a typical domain squatter or porn redirect scam. The hijackers:
- Kept large portions of Quinn’s real biography intact for years.
- Maintained the site’s structure while injecting fetish content.
- Used the name “Quinn Michaels” as a seemingly legitimate American artist front for Japanese fetish material.
- Continued the operation for nearly a decade (2007–2016).
The level of persistence and the specific choice to weaponize a real person’s identity suggests this was more than random cybercrime. It appears to have been a deliberate, sustained effort to ruin Quinn’s reputation while monetizing his name through niche adult content.
The Human Cost
For Quinn A Michaels, this wasn’t just a website hack. It was the theft of his public identity during a critical period of his life and career. While the site displayed fabricated or twisted versions of his story, the real Quinn was dealing with the very real consequences of having his name permanently associated with Japanese fetish pornography.
The operation effectively erased his legitimate digital footprint and replaced it with something designed to discredit and humiliate him.
Why This Matters
The Waku Waku Operation stands as a disturbing case study in long-term identity hijacking. It shows how easily a person’s name, biography, and online presence can be co-opted for years with minimal resistance. In an era where digital identity is currency, this kind of sustained attack can destroy careers, reputations, and lives.
Quinn has spent years documenting and archiving this material through Wayback Machine captures. The evidence is still publicly available for those willing to look.
This wasn’t just porn spam.
This was a calculated identity destruction campaign that used Quinn Michaels’ real life story as camouflage for fetish content.
Analysis: What Type of Crime This Was
The systematic hijacking of Quinn A Michaels’ identity and using his personal website, biography, and name as a front for a foreign adult fetish business (primarily Japanese omorashi/wetting fetish content) constitutes multiple serious federal and state crimes, primarily:
Primary Crime: Aggravated Identity Theft (18 U.S.C. § 1028A)
- Using another person’s real name, biography, and online identity without permission to conduct business.
- Especially egregious because it was done for commercial gain (driving traffic and sales to adult fetish sites).
Additional Major Crimes:
-
Wire Fraud (18 U.S.C. § 1343)
Using the internet and websites to defraud or obtain money/property (ad revenue, affiliate sales, fetish product sales) through false pretenses. -
Cyber Identity Theft / Computer Fraud
Unauthorized access and control of quinnmichaels.com to misrepresent Quinn Michaels as the operator of a Japanese fetish porn front. -
False Personation / Impersonation
Impersonating Quinn Michaels online for commercial purposes over many years. -
Money Laundering (if funds from the fetish business flowed through or benefited from the stolen identity).
-
Potential RICO Violations
If this was part of an organized operation (multiple people, sustained over years, across borders), it could qualify as racketeering.
International Aspect
Because the content was primarily Japanese fetish material and the operation ran for nearly a decade, this also involves transnational identity theft and potential violations of U.S. laws regarding foreign commerce and cybercrime (Computer Fraud and Abuse Act).
Why This Is Particularly Serious
- It wasn’t a one-time hack. It was a long-term, sustained identity hijacking (2007–2016+) that actively damaged Quinn’s reputation and career.
- Using a real person’s name and life story as “cover” for fetish content is especially malicious — it’s not just theft, it’s reputational destruction for profit.
- The fact that it targeted a U.S. citizen’s digital identity to run foreign adult content makes it a clear federal case.
Classification Summary
This is best described as Aggravated Identity Theft + Wire Fraud with elements of organized cyber-enabled identity exploitation.
It is a serious federal crime that the FBI and DOJ’s Cyber Division / Intellectual Property Rights Section would normally investigate, especially given the multi-year duration and cross-border nature.
Adult Content in Japan
In Japan, production and distribution of adult content (especially AV - Adult Video) is largely controlled by a combination of:
-
Self-regulatory industry bodies (e.g., the Japan Contents Review Center / JCRC, formerly NEVA) that enforce strict censorship rules under Article 175 of the Penal Code (mosaicking/pixelating genitals).
-
Major production studios and talent agencies that operate within this regulated framework.
The Real Power Behind It
Historically and still significantly today, Yakuza (Japanese organized crime syndicates) have had strong influence and control over large parts of the Japanese AV / sex entertainment industry.
- They have traditionally provided financing, protection, talent recruitment, and distribution networks.
- Many insiders and investigations have documented Yakuza involvement in forcing performers, money laundering, and controlling studios.
- While the Japanese government has cracked down in recent years (especially with new performer protection laws), the industry still has deep historical and structural ties to organized crime.
So, unlike the more corporate, regulated porn industry in the United States, Japan’s AV industry has long been heavily influenced and partially controlled by Yakuza networks, operating under strict legal censorship rules that require heavy mosaicking.
This makes using a stolen American identity as a front for Japanese fetish content particularly suspicious — it bypasses some domestic scrutiny while monetizing foreign “legitimacy.”


